Why TP-Link HTTPS web interface is detected as unsecure by some web browsers?
When logging in to TP-Link devices' Local Management via HTTPS to stay extra safe, some web browsers still report 'Not Secure'. The error message reported by some web browsers for TP-Link Local Management would be like the following picture:
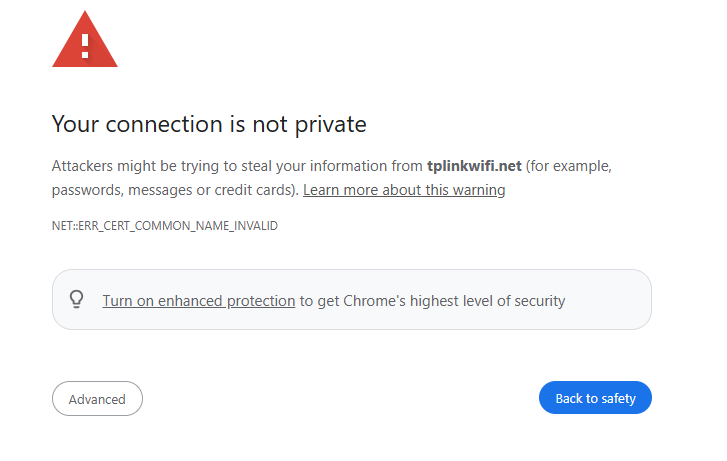
The reason why our browsers recognize TP-Link Local Management as "not private" is that TP-Link Local Management's Certificate is a self-signed Certificate. Most browsers do not accept this kind of Certificate because it is not an authoritative CA.
However, even if our self-signed Certificate is not trusted, the connection between your browser and the TP-Link devices' Local Management is secure.
A Certificate's purpose is only to allow a client to verify an unknown server. It has nothing to do with the encrypted connection. The data transmitted between the browser (client) and TP-Link Local Management (server) remains safe and encrypted. No one else could decrypt the data except the client and the server, because TP-Link Local Management uses TLS v1.2 as a secure connection builder. TLS v1.2 is a widely recognized secure connection protocol.
Take an example, in our Chrome browser, access tplinkwifi.net and press "F12" on the keyboard, switch to the "Privacy & Security" > "Security" tab, you will see the following information:
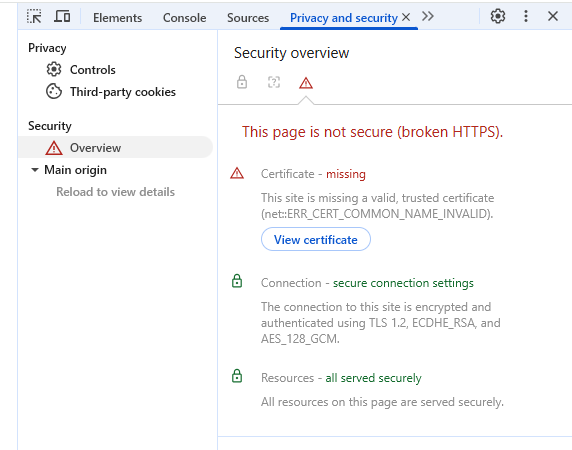
From Chrome's security report, it is obvious that tplinkwifi.net is using TLS v1.2 and the connection is secure. We do not have to worry about the safety of our computers and router.
Notes: Finding more about CA and how CA works:
Is this faq useful?
Your feedback helps improve this site.
TP-Link Community
Still need help? Search for answers, ask questions, and get help from TP-Link experts and other users around the world.