How to configure Shrew Soft VPN Client with a TP-Link VPN Router using the new GUI
With Client to LAN VPN function, the VPN Router will be a VPN server and we can use our PCs to establish the VPN tunnel with it. Then we can access the private network of the VPN Router securely via the internet. But we need to use some VPN client software like Shrew.
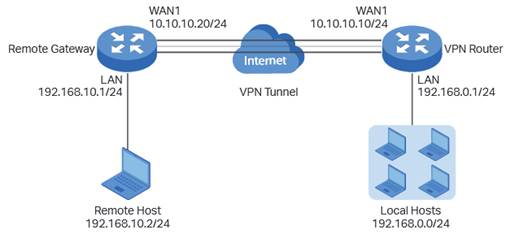
Take the following topology as an example, we will learn how to configure the VPN server and VPN client.
Step1 Verify the settings needed for IPsec VPN on router
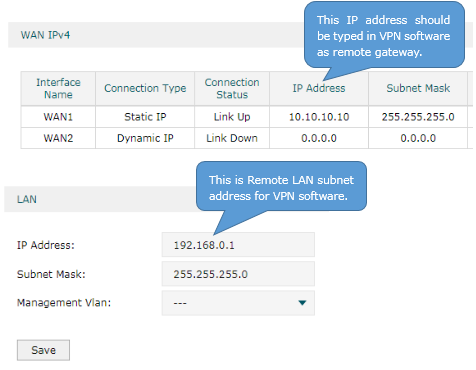
Check the VPN Router.
Choose the menu Status > System Status and Network > LAN.
Step 2 Set up the IPsec VPN Server
(1) Choose the menu VPN > IPSec > IPSec Policy and click Add to load the following page on the VPN router. Configure the basic parameters for the IPsec policy.
· Specify the mode as Client-to-LAN.
· Specify the Remote Host as 10.10.10.20. You also can enter 0.0.0.0 to allow any IP address.
· Specify WAN as WAN1 and local subnet as 192.168.0.0/24.
· Specify the Pre-shared Key as you like. Here we enter 123456.
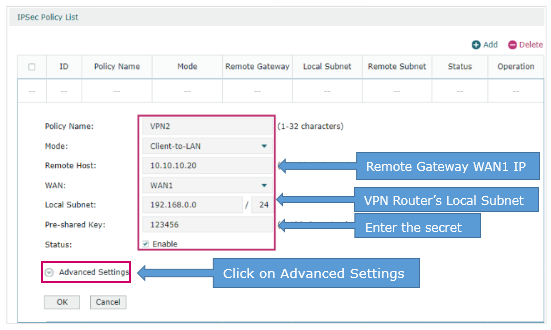
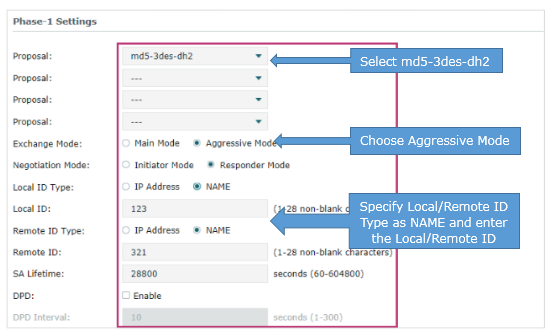
(2) Click Advanced Settings to load the following page. In the Phase-1 Settings section, configure the IKE phase-1 parameters.
· Select md5-3des-dh2 as the proposal.
· Specify Exchange Mode as Aggressive Mode.
· Specify Negotiation Mode as Responder Mode.
· Specify Local/Remote ID Type as NAME.
Once the VPN server or client is behind a NAT device, we have to select Aggressive Mode as Exchange Mode and select NAME as Local/Remote ID Type, otherwise, the VPN tunnel can’t be established.
· Specify the local/remote ID as you like. Here we specify the local ID as 123 and remote ID as 321.
(3) In the Phase-2 Settings section, configure the IKE phase-2 parameters. Click OK.
· Specify Encapsulation Mode as Tunnel Mode.
· Select esp-md5-3des as the proposal.
Once the VPN server or client is behind a NAT device, the proposal cannot be specified as ah-md5 or as –sha1, otherwise, the VPN tunnel can’t be established.

Step 3 Set up the IPsec VPN Client
(1) Click on Add. Choose the menu General. Specify Host Name or IP Address as 10.10.10.10. Select disabled as Auto Configuration. Select Use an existing adapter and current address as Adapter Mode.

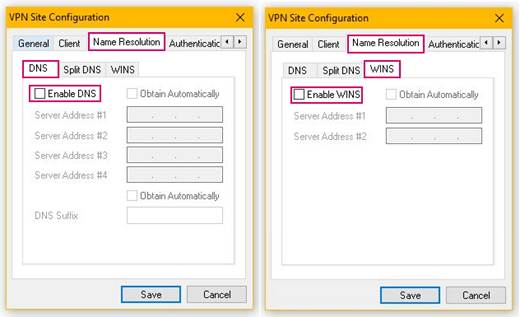
(2) Choose the menu Name Resolution, don’t tick the Enable DNS and the Enable WINS.
(3) Choose the menu Authentication. Select Mutual PSK as Authentication Method. Select Fully Qualified Domain Name as Identification Type. Specify 321 as FQDN String in Local Identify section and specify 123 as FQDN String in Remote Identify section.

(4) Choose the menu Authentication > Credentials. Specify Pre Shared Key as 123456.

(5) Choose the menu Phase 1, under the Proposal Parameters, the Exchange Type, DH Exchange, Cipher Algorithm, and Hash Algorithm are the same with VPN Router’s, we use aggressive, group 2, 3des, md5 here.

(6) Choose the menu Phase 2, under the Proposal Parameters, the Transform Algorithm, HMAC Algorithm are the same with VPN Router’s, we use esp-3des, md5 here. PFS Exchange and Compress Algorithm are disabled.

(7) Choose the menu Policy, don’t tick Obtain Topology Automatically or Tunnel All. Then click on Add. Select Include as Type, enter the VPN Router’s LAN Subnet Address and Subnet Mask, it’s 192.168.0.0, 255.255.255.0. Then click on OK and Save.

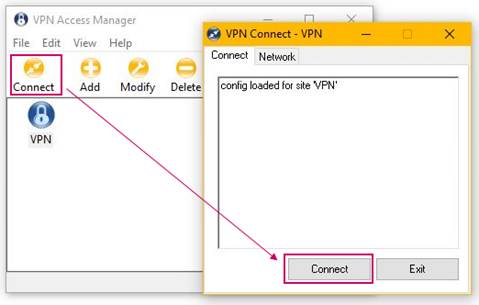
(8) Click on Connect.
Step 4 Verify the connectivity of the IPsec VPN Tunnel.
Choose the menu VPN > IPsec > IPsec SA to load the following page. If the IPsec VPN tunnel is established successfully, it will be shown in the list.

A fost util acest FAQ?
Părerea ta ne ajută să îmbunătățim acest site.







