How to prevent ARP Cheat or Attack
In network the Address Resolution Protocol (ARP) is the standard protocol for finding a host´s MAC Address when only its IP Address is known. Via modifying IP Address or MAC Address to achieve ARP cheat, it will be a large challenge for data transmitting normally.
From the way of affecting network connection, there are two possible ARP attacks, one is cheating router and other one is cheating computers. Of course, the two attacks may occur at the same time. Anyhow, once there is ARP cheat in network, the data between computers and router will be sent to wrong MAC Address and the connection can’t establish normally.
How do we prevent ARP cheat? As the two cheat ways, we have to prevent ARP cheat both on router and computer.
What do I need to prepare before setting preventing ARP cheat?
When you enable ARP cheat preventing function (IP Address & MAC Address binding) on TP-Link Router, you’d better do not obtain IP Address dynamically on your computers, as it will obtain different IP Address with the one in IP Address & MAC Address binding entry. Please set static TCP/IP properties on your computer.
Step 1
Assign static TCP/IP properties on your computer manually. Please go to our website and check configuration for How to configure TCP/IP Properties of my computer to connect to TP-Link router .
Step 2
Disable DHCP Server on the router after you login the Web-based Utility of it.
(1) Click DHCP-DHCP Settings on the left page.
(2) Select DHCP Server as Disable.
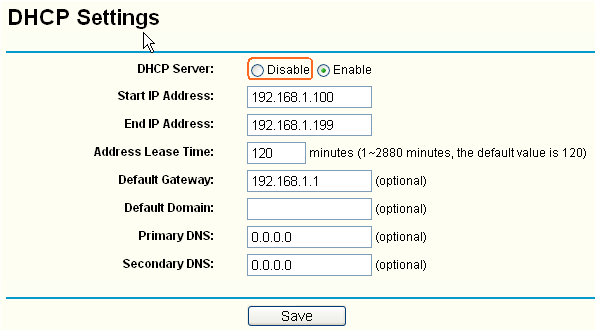
(3) Click Save to save settings.
How to set on the router to prevent ARP cheat?
Step 1
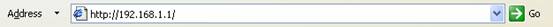
Open the web browser and type the LAN IP address of the router in the address bar, the default IP address of TP-Link router is 192.168.1.1/192.168.0.1, and then press Enter.
Step 2
Type the username and password in the login page, the default username and password both are admin.
Step 3
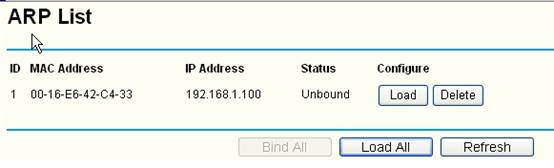
Click IP & MAC Binding->Binding setting on the left page.
Step 4
Select Enable ARP Binding, and click Save.
Step 5
Click ARP List on the left page, you can see ARP table the router learns.
If you can confirm the ARP table is correct, please click Load Add and Bind All, then all IP Address and MAC Address of your computers showed on the ARP table will be binded.
But if you can’t confirm the ARP table is no problem, please add IP Address and MAC Address of your computers manually.
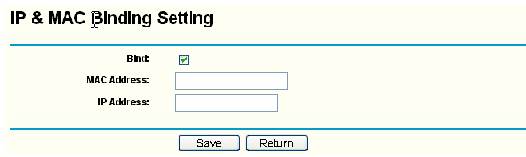
(1) Click Add New to set IP & MAC Bingding.
(2) Enable Bind, and type the MAC Address and IP Address of your computer.
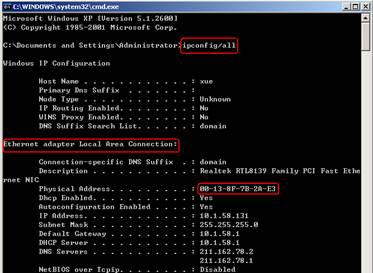
You should know the MAC addresses of the computers which you would like to allow them to access the Internet.You can check them on the computers with command prompt.
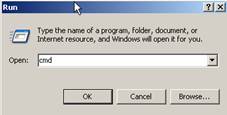
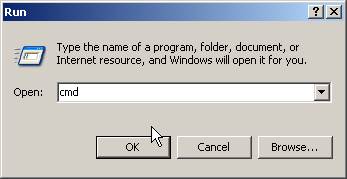
(1)Click Start->Run, type cmd and press Enter.
(2) Type ipconfig/all at the prompt window, press Enter, it will show the MAC address and other address information of this computer.
Step 6
Click Save to save the settings.
How to set on computer to prevent ARP cheat?
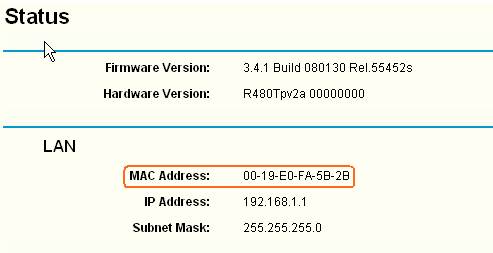
At first you should know MAC Address of the router, you can check the information on LAN
Status after you login Web-based Utility.
ARP command program is built-in on Microsoft Operation System, we can use it on prompt command.
Step 1
Click Start->Run, type cmd and press Enter.
Step 2
Type arp –s 192.168.1.1 00-19-e0-fa-5b-2b on the window and press Enter.
192.168.1.1 is router’s IP Address and 00-19-e0-fa-5b-2b is router’s MAC Address. Then type arp –a on the window, we can check the type of entry we add is Static.
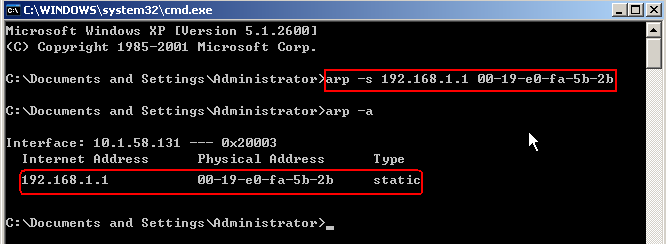
Till now, we have added static arp binding entry on computer then the data to router won’t be sent to wrong place. But we will find the entry will disappear after computer rebooting and we need to type the command again.
How can we do to make it running automatically without typing command manually every time?
Step 1
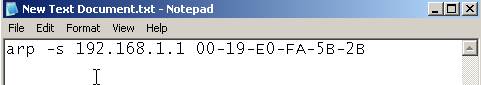
We need to create a batch file with extension name which is .bat, such as static_arp.bat, and edit it. Please type ARP command on it to bind IP Address and MAC Address of the router on your computer, then save it.
Step 2
Then click Start->All Programs, double click Startup, locate the batch file static_arp.bat in the folder.

After doing this, it will run arp command automatically when the computer reboots every time.
If you want to do more settings to protect your network from potential attacks. Please click:
Est-ce que ce FAQ a été utile ?
Vos commentaires nous aideront à améliorer ce site.